
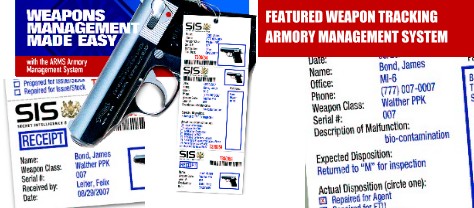
Combat Universal Weapons Tracking Software allows for weapons accountability, chain-of-custody control, bar code and RFID tracking and much more in one easy-to-use package
- Optimal security, peak performance and low cost of ownership
- Developed using state-of-the-art Java and Open Source software tools, with no third-party software licenses required
- No costly upgrades and maintenance in the future. The database, user interface, tags, electronic forms and workflow are customized around the specific requirements of each customer, providing powerful performance and ease of use.
- Workstations only require Java, and the server software is just 6.0 MB Server software includes: Java/Linux/Jboss/MySQL/Apache/Tomcat
Please contact us for a demonstration appointment. Demonstrations are now available.
BULLET-PROOF MANAGEMENT OF WEAPONS, GEAR AND ACCESSORIES
Weapons accountability, chain-of-custody control, plus bar code and RFID tracking
- Easily respond to incoming
requests to provide:
- New weapons, gear
and accessories to staff in various
locales - Weapon repairs and
maintenance, including technical
inspections and factory repairs - Transfer of existing
weapons from one location or owner
to another - Destruction of old weapons that are no longer serviceable
- Return of weapons to inventory when staff retire or quit
- New weapons, gear
and accessories to staff in various
USE RFID (RADIO FREQUENCY) OR BAR CODE LABELS FOR RAPID INVENTORY CHECKS
- Any weapon within a few feet of an RFID reader will be inventoried and associated with the location from which the inventory is taking place
- Missing weapons’ serial numbers can be entered into a portable RFID reader and will “beep” if the reader comes within a few feet of the weapon for which the search is being conducted
CUSTOMIZED LOCATION AND STATUS MENUS MAKE CHAIN-OF-CUSTODY VERIFICATION SIMPLE
- Maintains a complete audit trail detailing a weapon’s history from active to retired to destroyed
- Built-in weapon location control screen enables individual or batch processing of weapons being received, assigned or transferred
- Customized queues to monitor weapon locations,inspection, repair cycles and parts usage
AS “TOP SECRET” AS YOU NEED IT TO BE
- User access can be granted at four different security levels
- Data fields can be secured so only Administrators can view sensitive user information (Social Security numbers, etc.)
- Customized reports are
available, detailing weapons transferred or repaired by time periods
All products and services are available on GSA Schedule GS-07F-0661W to the US Federal Government applications.
combatweaponstorage.com, gsaweaponstorage.com, weaponstorage.com